At the Security Analyst Summit that took place on September 30,2021, during which the security company Kaspersky Lab released a report on a new cyber espionage group called GhostEmperor who have been using new techniques to launch cyberattacks on servers.
The main target of GhostEmperor is government and telecommunications services in Malaysia, Thailand, Indonesia even spanning all the way to Afghanistan and Egypt.
It is being said that the group is focused on gaining long term access to its victims and uses a highly sophisticated toolkit that is even compatible with Windows 10 further increasing the risks.
GhostEmperor entered servers through applications such as Oracle and Microsoft Exchange whose servers were exploited by the group to enter the target servers.
In the report, they have detailed how GhostEmperor uses different scripts and tools to help infiltrate the network’s backdoors.
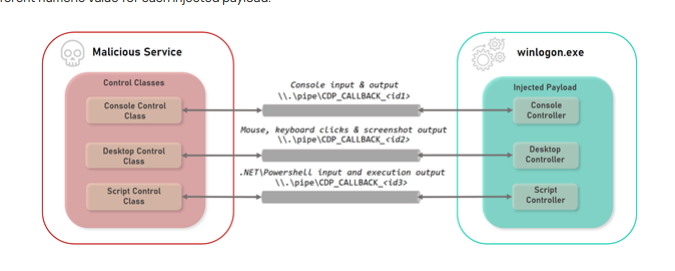
Courtesy: Kaspersky
After infiltrating the network, the backdoor is used to install the open-source Cheat Engine which is primarily used by gamers to install cheat codes to their games. This was then used to install a very powerful rootkit called Demodex to their server.
The toolkit is developed in such a manner that it continues to stay on the system even after the operating system is reinstalled and updated to Windows 10.
The main reason why this group sticks out is because the group seems to be using anti-forensics and anti-analysis tools that caused a hindrance to security researchers who were trying to analyse their malware.
They also packaged fake data and sent it to the command rather than sending the real things. This kind of sophistication that GhostEmperor displays is something to keep your eye on.